Outcomes | Modernization
Hybrid PAM
Extend Privileged Access Management across multi-cloud and on-premises systems. Consistent governance, without the complexity.

Modern production environments demand controls that keep pace.
Legacy PAM tools were built for a world of static, on-premises infrastructure. As production environments stretch across AWS, Azure, GCP, and traditional data centers, those tools begin to fracture; creating coverage gaps, inconsistent policies, and growing credential sprawl. Teams end up managing multiple systems without a central view of who has access to what and why.
P0 Security provides a central control plane for modern privileged access management that scales with your sensitive systems as they evolve and grow.
The problem
PAM coverage breaks at the hybrid boundary.
Most organizations did not choose hybrid infrastructure, they accumulated it. Cloud resources were provisioned alongside existing on-premises environments, and the PAM tools that governed one environment rarely extended cleanly to the other. The result is fragmented governance: strong controls in one environment, blind spots in the next, and no unified way to measure or report on either.
Access policies are siloed across environments
No unified visibility into who holds what privilege and why
Credentials multiply without standardized governance
Inconsistent policy enforcement across sensitive systems
The solution
Unified privilege governance across every infrastructure layer.
P0 Security extends modern PAM governance across your entire hybrid estate through a single control plane. The Identity Graph tracks every identity and access path; whether it lives in a cloud IAM service, an Active Directory, or a traditional server. JIT access, least-privilege enforcement, and full identity-bound audit trails work consistently regardless of where your infrastructure sits.
Global governance model for consistent policy enforcement at runtime
Automatic privilege discovery and mapping of access path across your entire estate
Identity-first audit trails simplify compliance reporting with built in ownership
Capability highlights
Bastionless JIT SSH for any server
Short-lived, IdP-tied credentials replace static SSH keys across both cloud and on-premises servers. No bastion hosts, no credential vaults, just governed, ephemeral access.
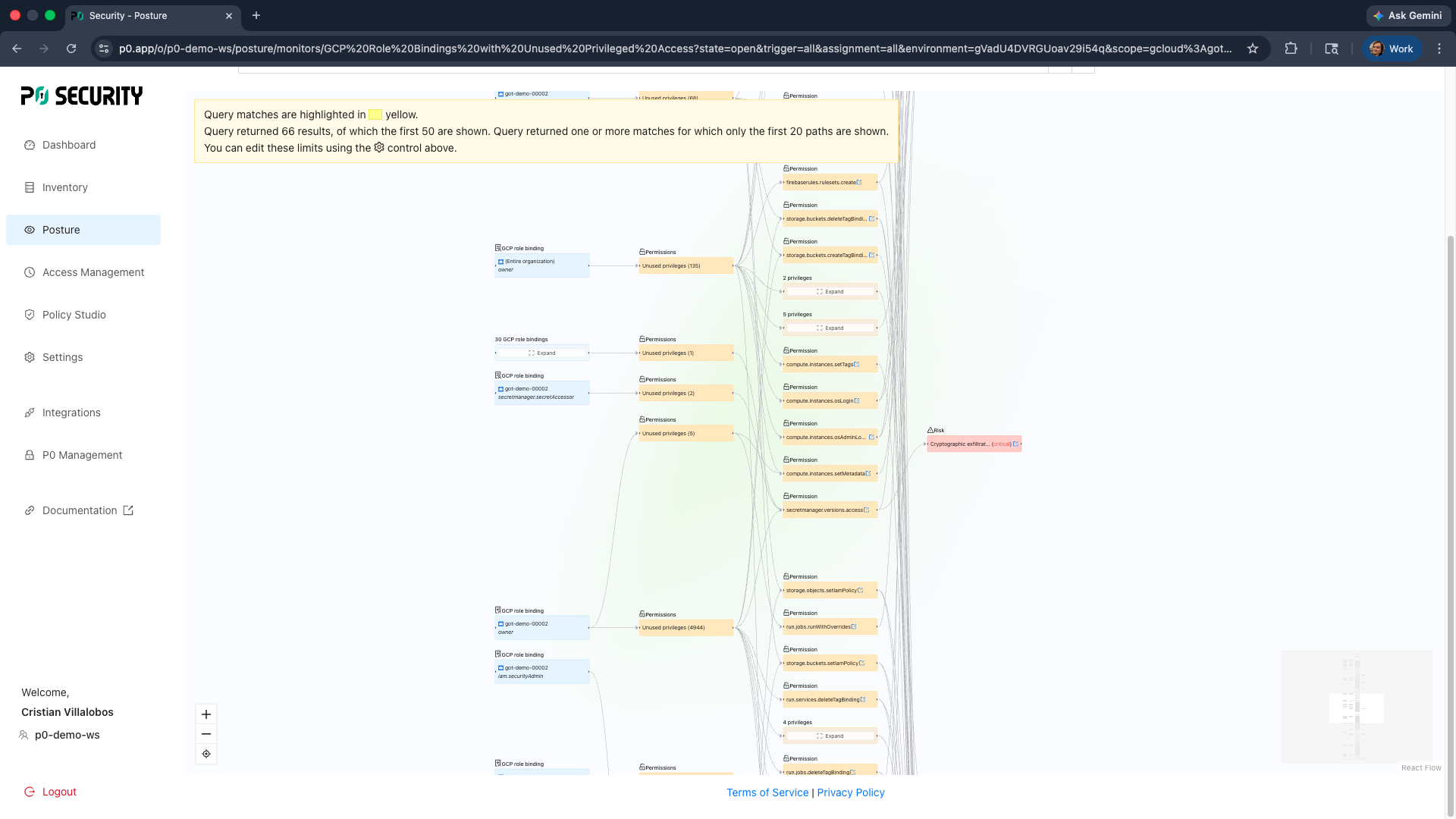
Access Graph across hybrid environments
A continuously updated map of every identity and entitlement across all privilege resources gives you a single source of truth for access governance.
Unified access request workflows
Engineers and developers request access the same way whether they need a cloud instance or an on-premises database; via Slack, CLI, or the P0 web console.