Outcomes | Privilege governance
Achieve Zero Standing Privilege
Eliminate static credentials and standing access across your entire identity estate, before they become your next breach vector.

Static credentials do not expire. Breaches do not either.
Standing privilege and static credentials are the most common preconditions for cloud security incidents. An API key provisioned two years ago, an SSH key never rotated, a service account with admin rights that no one remembers creating; these are the access paths that attackers find and exploit. Eliminating them requires a governance model that makes short-lived, least-privilege access the default and standing access the exception that must be actively justified. P0 Security provides exactly that model.
The problem
Standing privilege is what attackers count on.
More than 83% of cloud intrusions are rooted in identity compromise and in most cases those breaches are only possible because of standing privilege, persistent access that did not need to be there. Static credentials are the mechanism by which standing privilege persists: once issued, they remain valid until someone explicitly revokes them. In practice, that revocation rarely happens on schedule, if it happens at all.
Credentials remain valid indefinitely unless someone manually revokes them
Broad privilege is the operational reality; least privilege is just the stated policy
No way to distinguish active credentials from dormant ones
Humans, service accounts and agents all accumulate risky standing privilege the same way
The solution
Replace standing privilege with short-lived, governed access.
P0 Security's Zero Standing Privilege model closes the loop between access provisioning and access governance, replacing persistent credentials with short-lived grants that are automatically issued when needed and automatically revoked when they are not. The privilege governance module combines posture risk assessment, least-privilege remediation, and runtime policy conversion to systematically eliminate standing access across your entire identity estate.
Static credentials replaced with short-lived grants that expire between sessions
Continuous privilege assessment with automated remediation and just-in-time access policy conversion
Every access lifecycle managed in one closed loop so standing privilege cannot accumulate
Capability highlights
Zero Standing Privilege enforcement
The ZSP model replaces persistent access with short-lived, time-limited grants across human, machine, and AI agent identities; making least privilege the operational default across every environment.
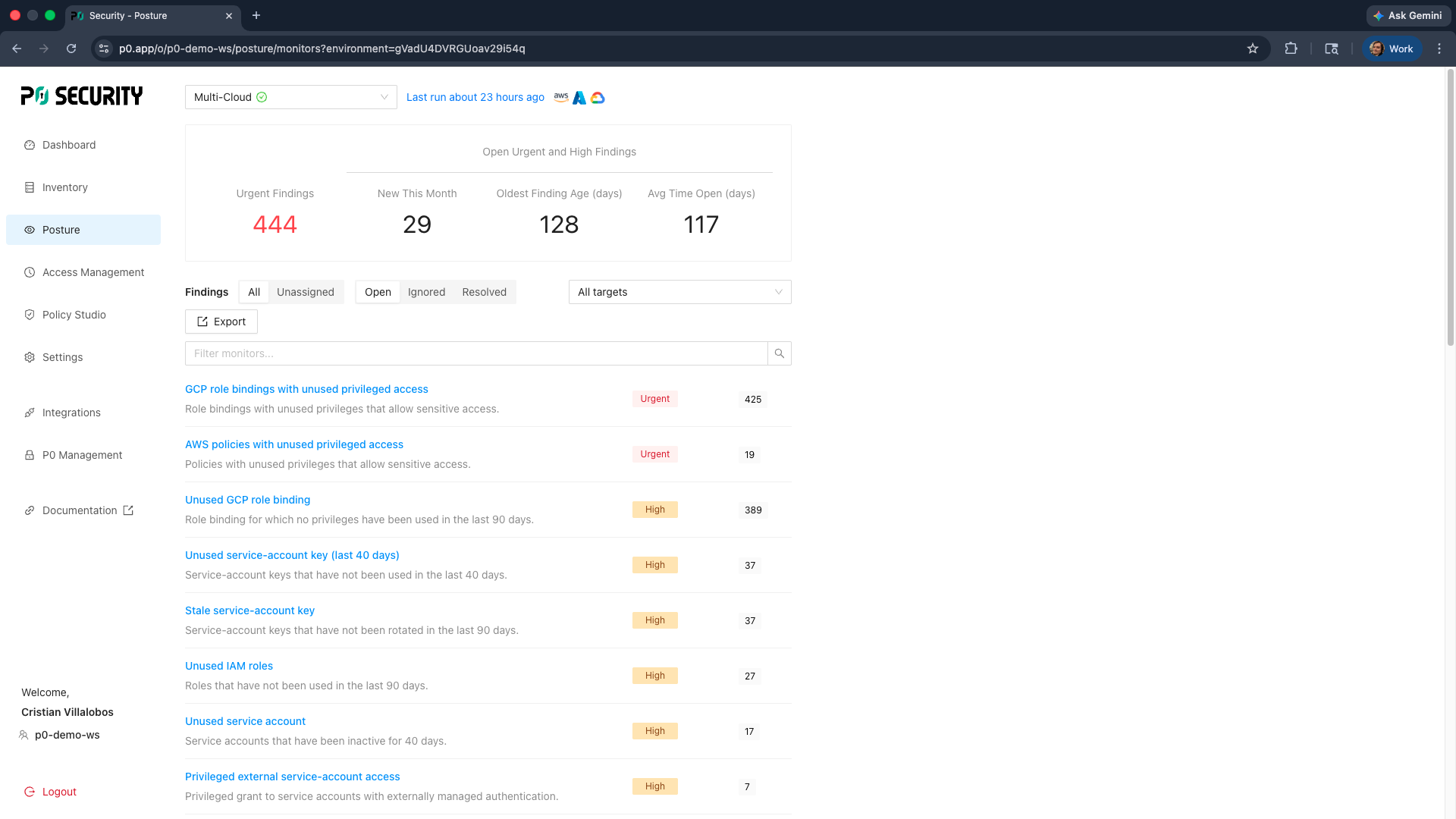
Privilege posture assessment
The privilege governance module continuously evaluates entitlements against least-privilege standards and surfaces risk-ranked remediation recommendations for over-privileged identities across your entire estate.
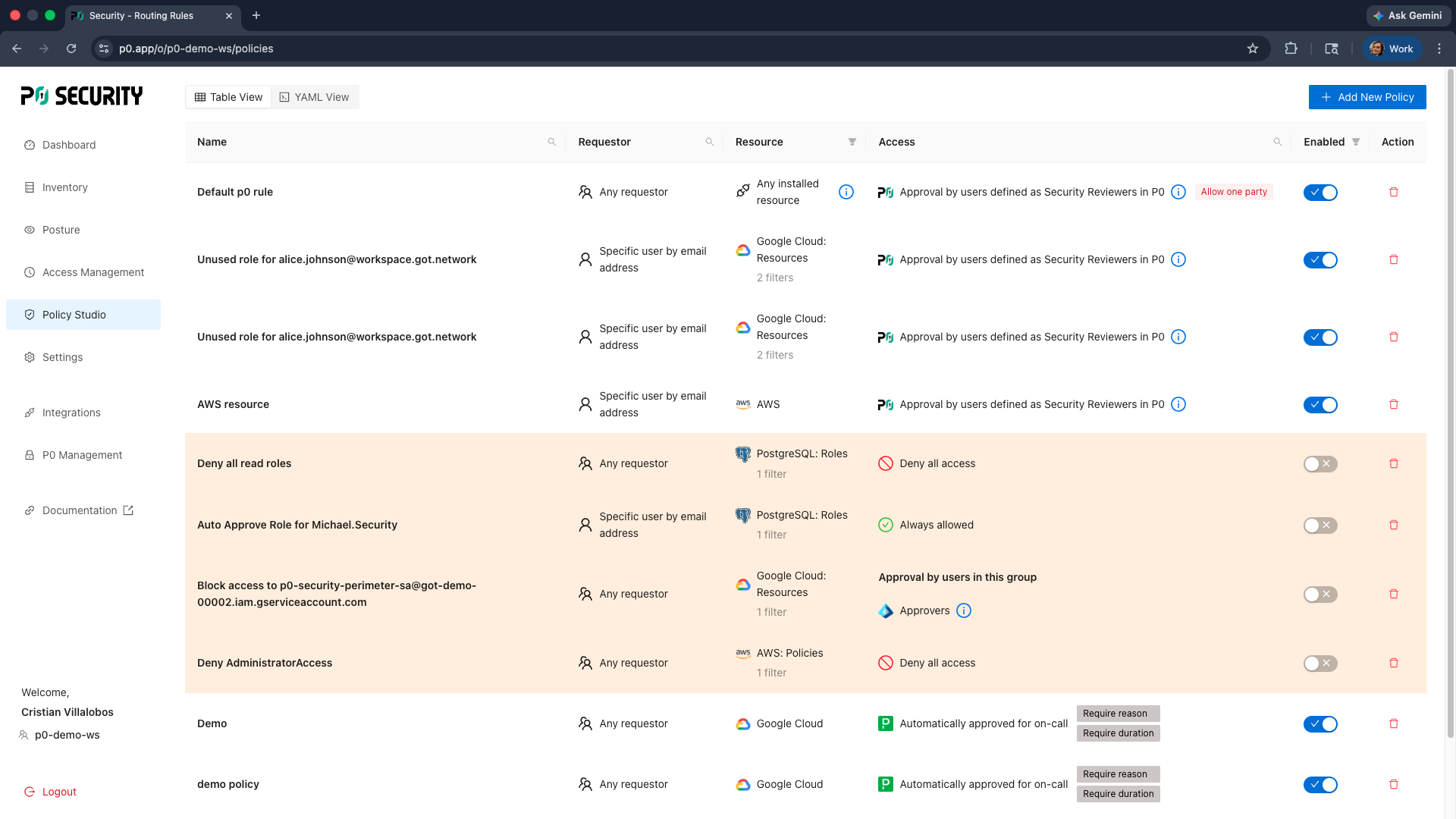
Runtime policy conversion
P0 converts standing access policies into just-in-time runtime policies without requiring manual rebuilding of access rules, accelerating the path from standing privilege to zero standing privilege.