Platform | Technology
For workloads
All machines, workloads and AI agents acting under the same central guardrails as the human users they represent.
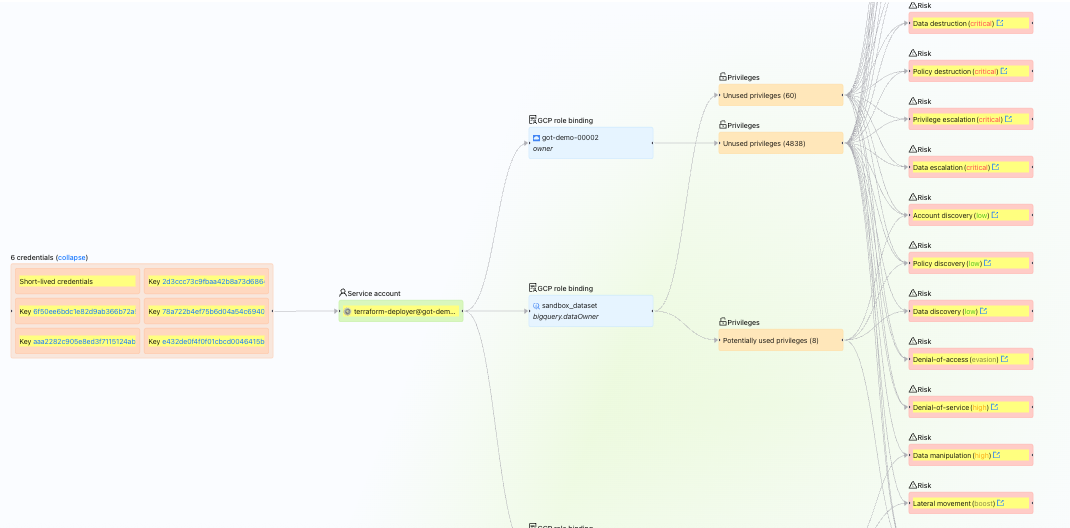
Over privileged and ungoverned.
Service accounts, workloads and automation pipelines now outnumber human users across most environments. They are often created quickly, over-scoped by default and rarely revisited. Many operate with persistent access, unclear ownership and limited visibility into what they can reach. As environments scale, this creates sprawling, unmanaged access paths and significant hidden risk across production systems.
Solution
Consistently govern every workload.
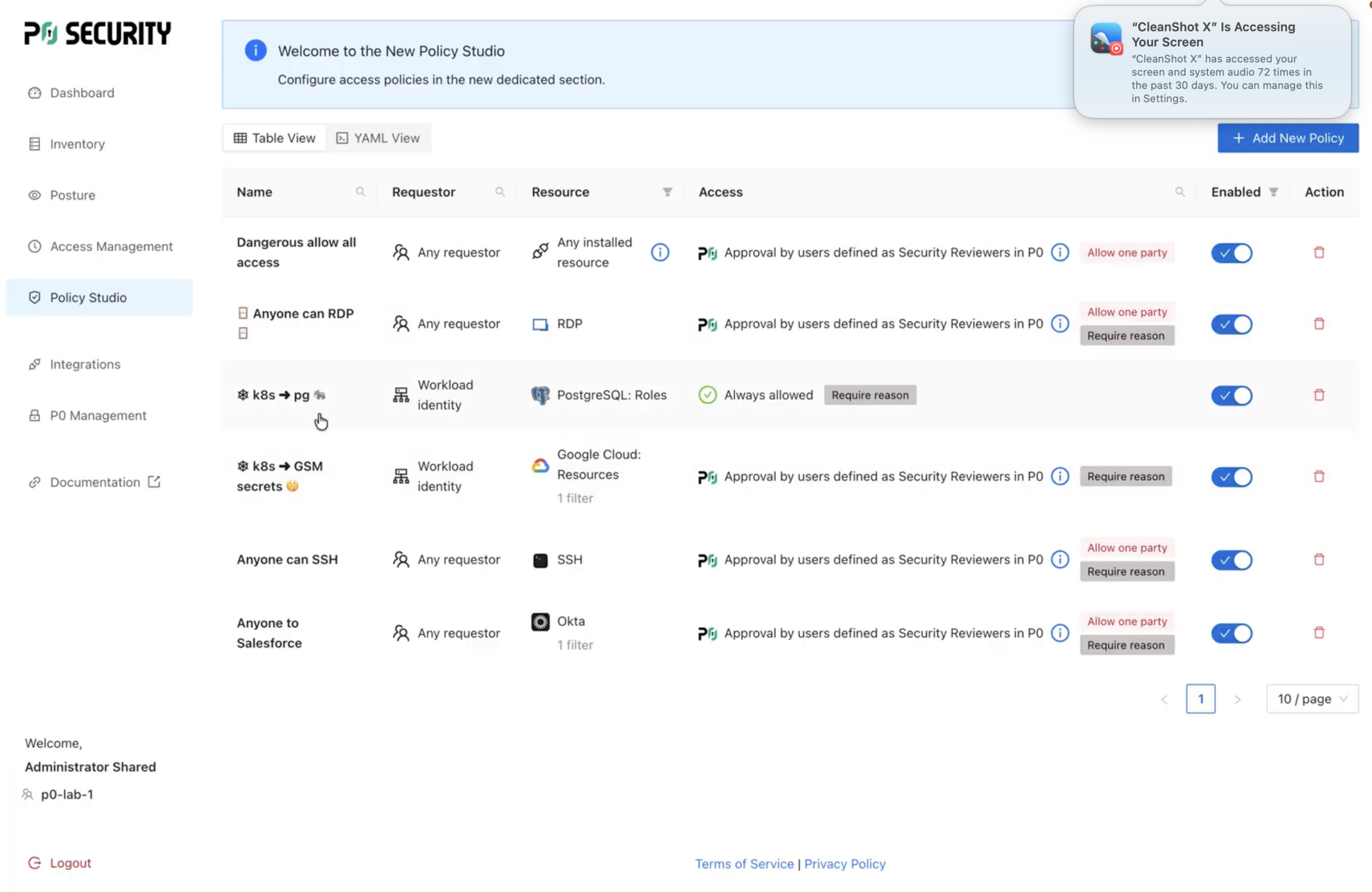
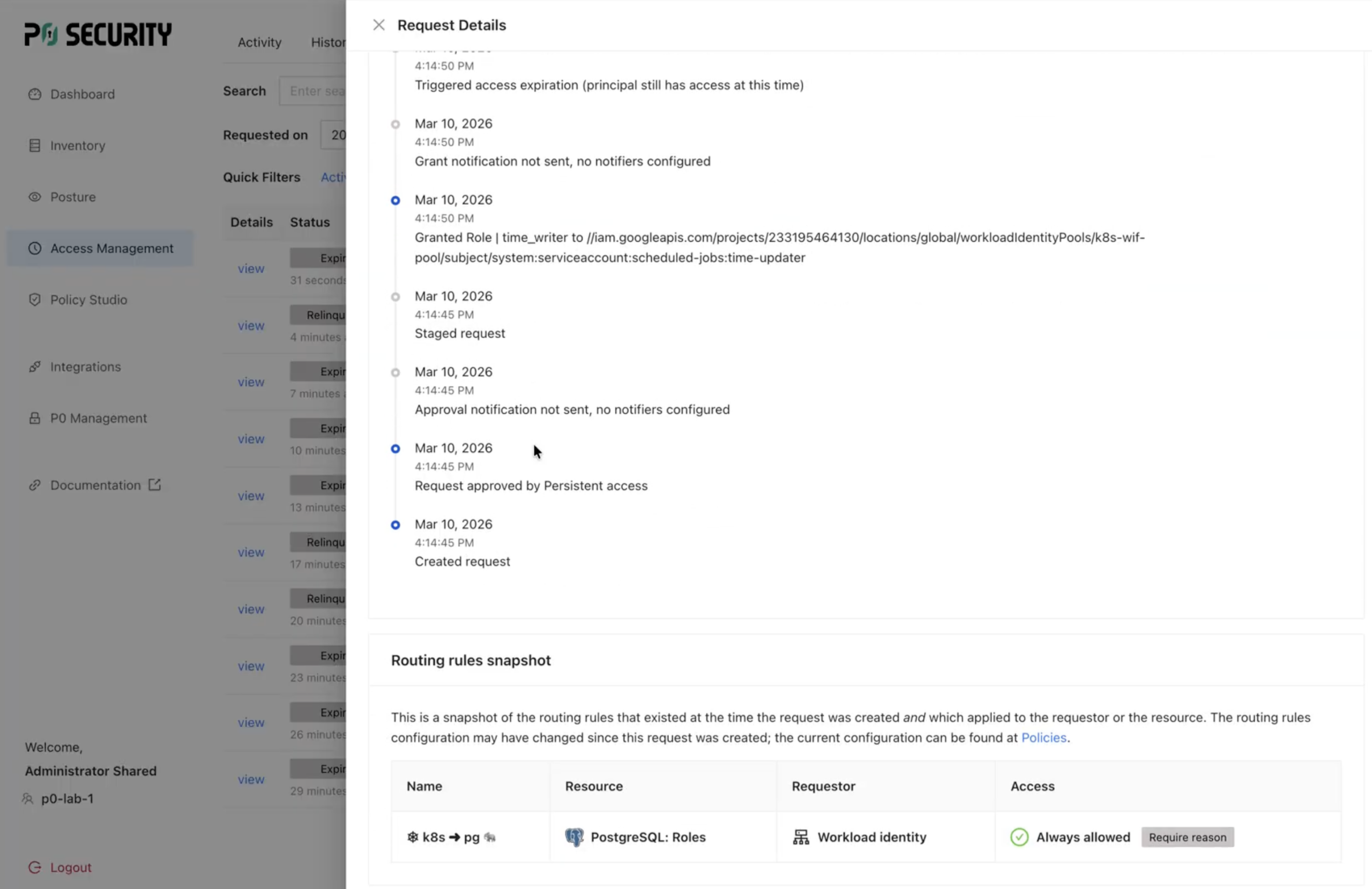
P0 replaces static credentials and fragmented tooling with centralized, policy-driven authorization. It continuously discovers non-human identities, maps what they can access and assigns accountable ownership. Access is granted just-in-time and scoped to intended usage, eliminating long-lived credentials while maintaining session-level audit trails.
Unified governance
When non-human identities are governed under the same model as users, access becomes intentional, controlled and auditable at scale.
Least-privileged, auditable and scalable control for every NHI.
P0 centralizes visibility, governance and enforcement for service accounts, workloads and automation. By applying a unified policy framework across all identities, P0 ensures access is continuously evaluated, tightly scoped and tied to accountable ownership.

Continuous discovery and visibility
Inventory all service accounts, workloads and agents and map their access across systems and environments.

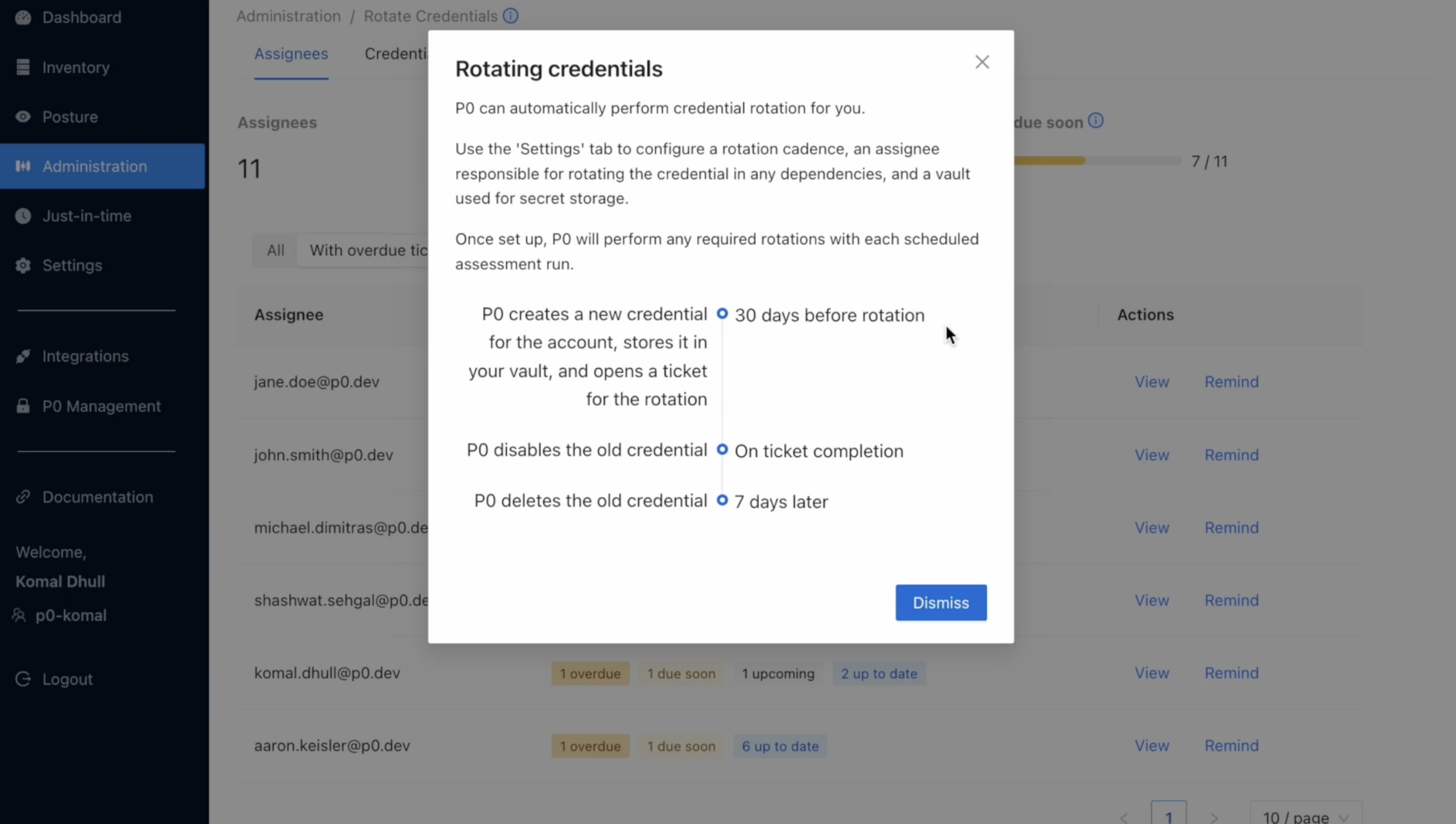
Policy-driven lifecycle management
Define usage intent, enforce least privilege and automate credential rotation to remove manual overhead.

Central governance and accountability
Tie all access back to a responsible user or team, streamlining governance, audit readiness and risk reduction.

“As we continuously anticipate what the business will need next, we have to enable agility in a way that doesn’t compromise security or operational resilience. P0 enabled us to scale our governance of non-human identities with automated, policy-driven controls; bringing service accounts, static credentials and their entitlements under the same disciplined guardrails we uphold for all privileged access.”
Michael Chan
Director of AI and IAM Security at CNA
“P0 enabled us to scale our governance of non-human identities with automated, policy-driven controls.”